Yahoo! rejected mail from my server one too many times and I've had enough.
Since you can't fight city hall (trust me, I tried; never ever got a meaningful response from Yahoo!) I figured I might as well swallow the pill and implement an outgoing e-mail security feature that Yahoo! relies on, DKIM (DomainKeys Identified Mail).
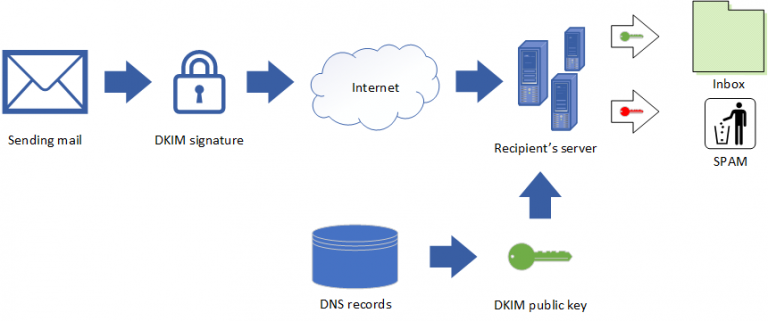
DKIM adds a cryptographic signature to outgoing e-mail, which can be verified in turn through a DNS record, as illustrated in this diagram:
I am indebted to Tom Huerlimann, whose very clear instructions were almost perfect; my own notes are based on his. Like him, I was installing DKIM on a CentOS 7 server. These were the steps:
1. Install opendkim
yum install opendkim
2. Edit /etc/opendkim.conf
The key lines to add/modify are:
...
Mode sv
...
KeyTable /etc/opendkim/KeyTable
...
SigningTable refile:/etc/opendkim/SigningTable
...
ExternalIgnoreList refile:/etc/opendkim/TrustedHosts
...
InternalHosts refile:/etc/opendkim/TrustedHosts
...
Everything else can stay the same. I was, in particular, caught by the Mode sv line; I neglected to change it from the default (Mode v, verify only) and the resulting behavior was tricky and misleading.
3. Modify /etc/opendkim/KeyTable
default._domainkey.vttoth.com vttoth.com:default:/etc/opendkim/keys/vttoth.com/default.private
4. Modify /etc/opendkim/SigningTable
*@vttoth.com default._domainkey.vttoth.com
5. Modify TrustedHosts
192.168.200.0/24
6. create /etc/opendkim/keys/vttoth.com/
7. Create key pair
opendkim-genkey -D /etc/opendkim/keys/vttoth.com -d vttoth.com -s default
8. Change ownership
chown -R opendkim.opendkim /etc/opendkim
9. Start opendkim
systemctl start opendkim; systemctl enable opendkim
10. Modify sendmail.mc
Append
INPUT_MAIL_FILTER(`opendkim', `S=inet:8891@localhost')
to the end of sendmail.mc; re-make sendmail.cf, restart sendmail.
11. Add all default.txt files to the appropriate DNS zone files; restart DNS
12. Check sent mail for DKIM signature
That's basically it. Actual parameters should of course be modified according to your needs. In my case, I run a mail server for multiple domains, so it was indeed necessary to mess with the configuration in this manner; simpler setups are possible.


